
Michael Buckbee
18 Oct 2023
Rack::Attack is fantastic (seriously, we even wrote the Ultimate Guide to Rack::Attack), but by design it's:
Standard Rack::Attack usage is:
It's a tedious process that relies on you coming up with security rules from scratch, and then, because it's config-based, it creates very brittle static rules that are almost immediately out of date.
While you can get creative with hacking in some dynamic rules, it's not a great experience and is not what Rack::Attack was designed for.
Similarly, if you're using Rack: :Attack for rate-limiting, it's challenging to determine if the limits you set are too high. Too low? Are they even working? You can't tell from the logs, and the lack of feedback exposes your app to abuse.
Designed to shrink the feedback window between your logs, requests, and rules, Wafris gives you the following:
 Wafris vs Rack::Attack Feature Comparison
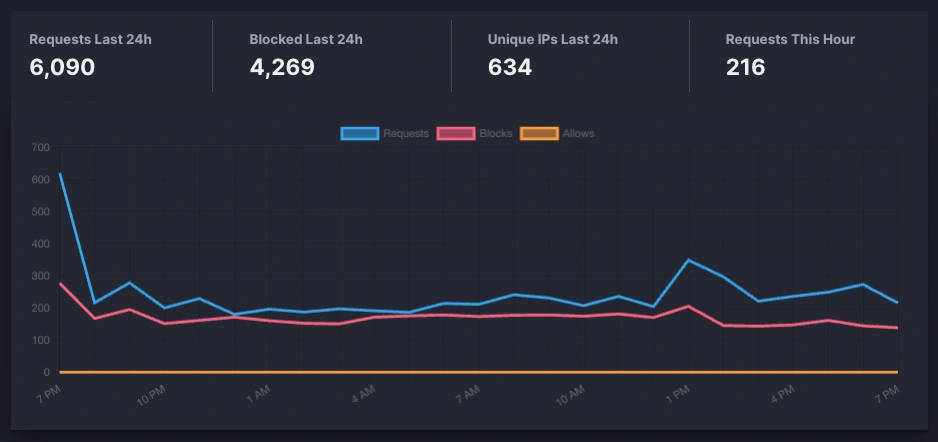
Wafris vs Rack::Attack Feature ComparisonWafris provides a dashboard that allows you to visualize the blocked traffic and the rules blocking it.
| Rack::Attack | Wafris | |
|---|---|---|
| No deploy rule setting | ||
| Block traffic | ||
| Requires Redis for rate limiting | ||
| Visualize blocked traffic | ||
| Visualize blocked traffic by rule | ||
| Visualize blocked traffic by path | ||
| Preset Rulesets | ||
| - Block IPs | ||
| - Block IP Ranges (CIDR) | ||
| - Block User Agents | ||
| - Block Hosts | ||
| - Block Paths | ||
| - Block Parameters | ||
| - Block Methods |
If you have Rack::Attack already installed, it can work side by side with Wafris.
# Gemfile
gem 'wafris'
gem 'rack-attack'
rake middleware and verifying that the Wafris::Middleware line shows up before the Rack::Attack line.And that's it! You can choose to keep all of your rules in Rack::Attack or start moving them over to Wafris. It's up to you.
Start blocking traffic in 4 minutes or less