
Michael Buckbee
10 May 2023
Most developers take IP addresses for granted until their site's under attack, log files are bursting, and they're frantically trying to work out where the threat is coming from.
Step one is to find which of the requests are threats and how to filter them out. That requires an IP lookup service, but one that's not designed for marketers. Instead, it needs to detect whether an IP is a bot, malware, or has a reputation for dangerous behavior.
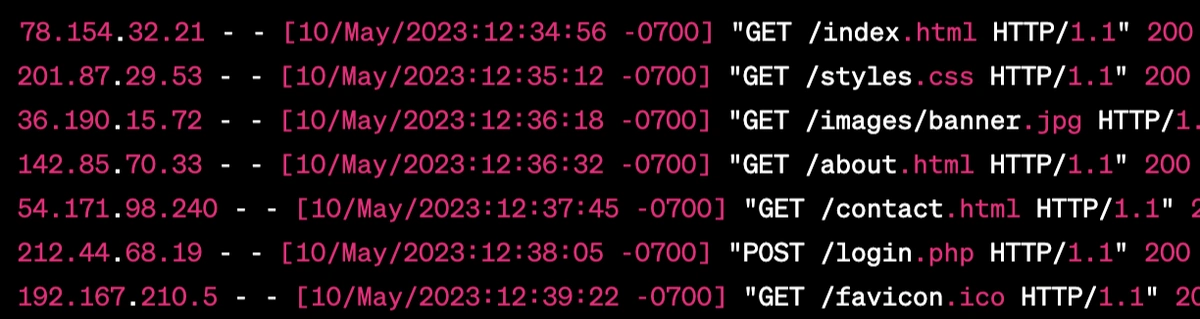
Which IP is actually a bot hiding behind a VPN?
We're acutely aware of the damage malicious traffic causes as we're on a mission to protect every web app on the Internet (with our open-source Web Application Firewall, Wafris).
Core to this is better IP lookup data to feed the WAF, so step 1 was to build a better IP lookup service explicitly designed to answer the burning question: "Is this IP a threat?"
Here's everything we're doing differently:
It's an ongoing effort, but we've created a model that grades each searched IP address to give you a quick sense of its risk.
The model is based on many factors, including country, ASN, IP reputation, bot activity, cloaking, and more.
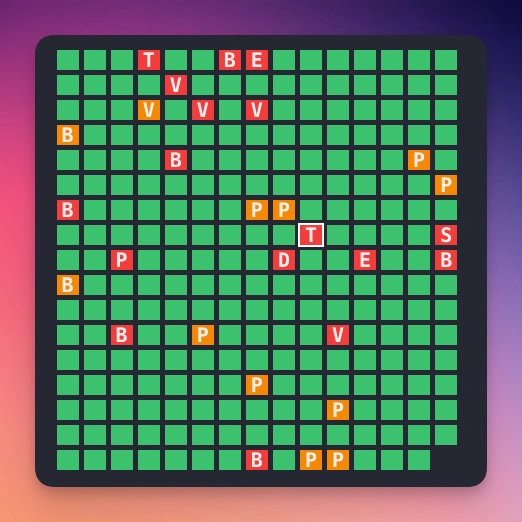
We've also created a network neighborhood for each searched IP address, so you can see what other IP addresses are nearby.
"Neighborhood" is a valuable concept, as a malicious IP address is often part of a larger block of bad IP addresses. Web hosts have different policies regarding hosting malware; some are significantly laxer (or even openly advertise that they'll host malware, bots, and spammers) than others.
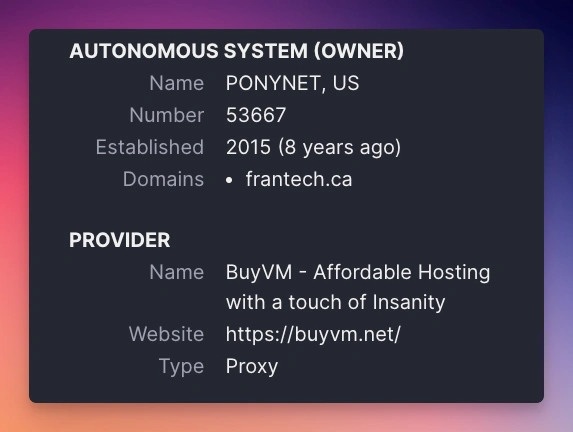
It can be helpful to determine what "type" of IP address you're dealing with: is this a residential IP address? A data center IP address? A VPN? A Tor exit node?
"Autonomous System" is the term used to describe a group of IP addresses that are all controlled by the same entity. If that entity has a policy of hosting malware, then it's likely that all of the IP addresses in that AS are also hosting malware.
Similarly, if you're concerned about VPNs, you can use the AS information to determine if a VPN provider owns the IP address.
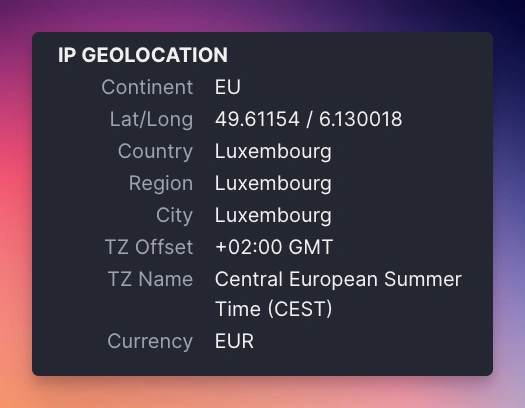
Geolocation is a tricky one. It's not strictly correlated with ASN as there are lots of global companies (e.g., Google, Amazon, Microsoft) that have IP address allocations all over the world.
The Geolocation data we provide isn't just the ASN location; instead on the IP address itself. We've found that this is the most accurate way to determine the geolocation of an IP address.
Security-wise - it's often the case that a disproportionate amount of attacks come from certain countries. For example, if you're a US-based company, you might want to block all traffic from Russia and China (for practical and sanctions reasons).
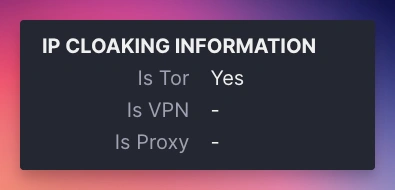
Threat actors often use cloaking techniques to hide their systems' actual location and make it harder to block them.
While there are absolutely legitimate security reasons to use cloaking techniques like VPN and Tor for both privacy and anonymity, it is also undeniably the case that these same technologies are widely abused to hide the origin of attacks.
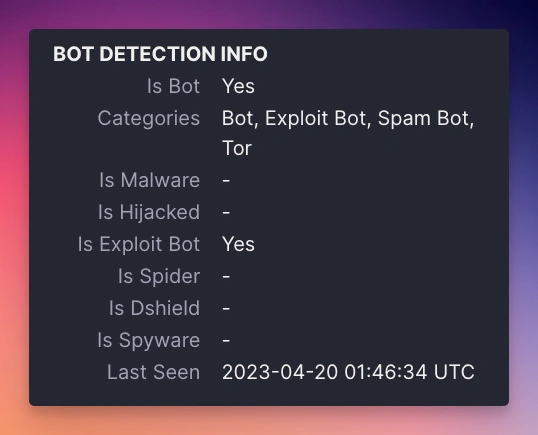
Bot activity is collected from our honeypots, but we also bring in many other sources to determine if an IP address is a bot.
Honeypots are servers set up in popular hosting providers and designed to look like vulnerable web applications.
When a bot hits one of our honeypots, we record the IP address and the type of attack.
Often these activities aren't directly harmful but are a "forward scout" to determine if a system is vulnerable to further attack.
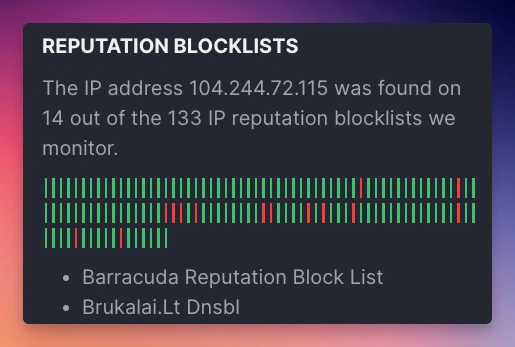
A mantra of mine is "security is a community activity" - we, the people building applications and sites and defending them from attacks, need to work together to share information about threats as there's a severe asymmetry to the attacker/defender relationship.
An attacker can trivially spin up an attack script hidden behind a bunch of proxies and hit thousands of sites in minutes.
Conversely, a defender has to manually investigate each IP address to determine if it's a threat.
Shared blocklists are a lever to help tip the scales back in the defender's favor, as the IP address hitting your site might have already been identified as a threat by someone else.
We're excited to launch the Wafris IP Lookup service as it's a key component of our mission to protect every web app on the Internet.
It's the first step in a long journey, and we're excited to continue to improve the service and add new features.
Please let us know if you have ideas on what we can improve with it or what we should add!
You can reach me directly at mailto:mike@wafris.org
Start blocking traffic in 4 minutes or less